Our weekly hack for those in the field doing the work & digging up critical intel.
 The ability to uncover information on the internet is the primary skill of an online investigator. There are hundreds of thousands of surface, deep, and dark websites, but which are most pertinent to your unique case? Do you know how to utilize Google to its full potential? With new social media platforms coming online at a rapid pace, capturing leads and evidence in social media networks is more complex than ever. Do you know the latest tools of the trade?
The ability to uncover information on the internet is the primary skill of an online investigator. There are hundreds of thousands of surface, deep, and dark websites, but which are most pertinent to your unique case? Do you know how to utilize Google to its full potential? With new social media platforms coming online at a rapid pace, capturing leads and evidence in social media networks is more complex than ever. Do you know the latest tools of the trade?
Hg’s OSINT Tips of the week provides you with the latest intel how to be most effective in our tradecraft. We are always looking for new tools, so don’t hesitate to let us know if you have one you’d like reviewed in a future post!
Enjoy!
This week, we provide a couple of valuable resources. One is for generating breach-resistant passwords and the other for sniffing out flaws in your online security presence. These platforms can be valuable for infosec activity—uncovering all kinds of ways to remain secure and safe. Come on, it’s time to dig in.
INFOSEC: strongpasswordgenerator.org
 Having a strong password can help prevent your accounts from being breached. Strong Password Generator is a good tool to use when generating a secure password for a routine account, or as a throwaway password for a one-time login. The resource allows for password qualifiers such as upper- and lower-case letters, numbers, symbols, and length of password. Simply copy and paste to the account in question without having to worry about reusing an old password. Keep in mind, a strong password should be used in combination with other security best practices such as two-factor authentication.
Having a strong password can help prevent your accounts from being breached. Strong Password Generator is a good tool to use when generating a secure password for a routine account, or as a throwaway password for a one-time login. The resource allows for password qualifiers such as upper- and lower-case letters, numbers, symbols, and length of password. Simply copy and paste to the account in question without having to worry about reusing an old password. Keep in mind, a strong password should be used in combination with other security best practices such as two-factor authentication.
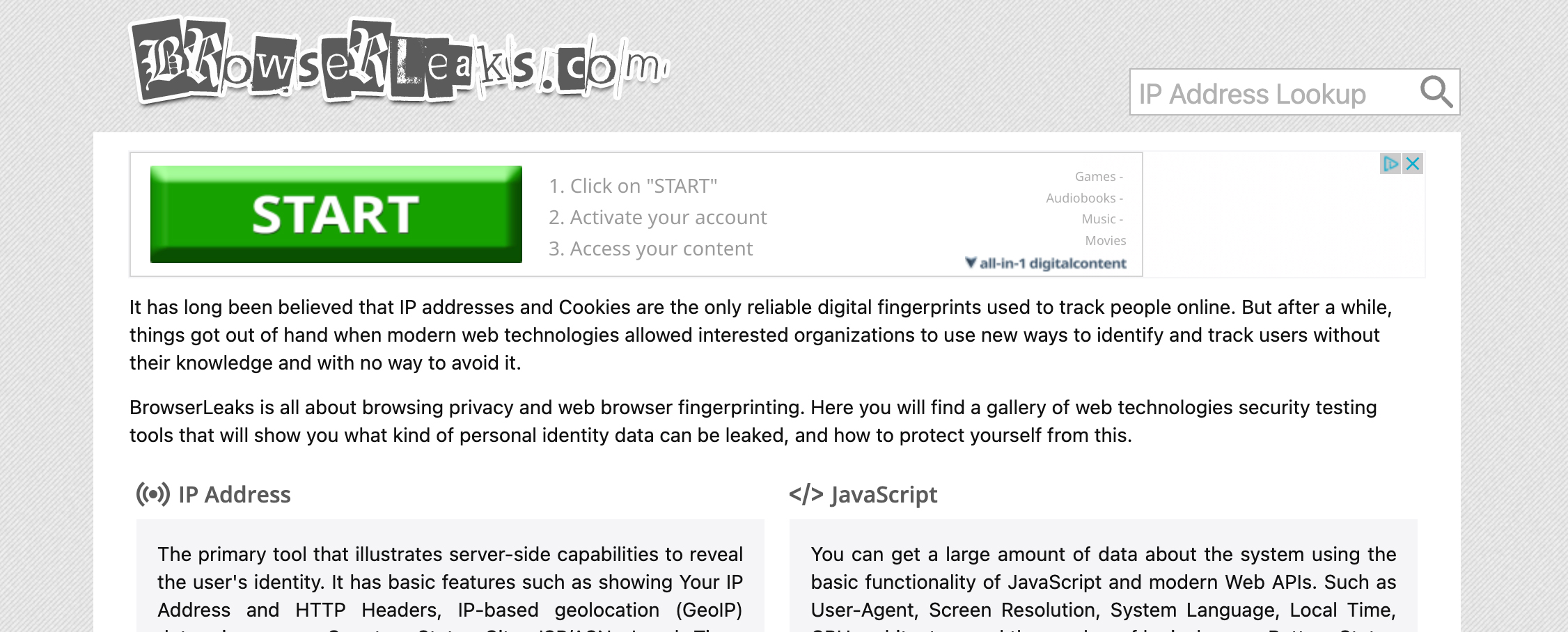
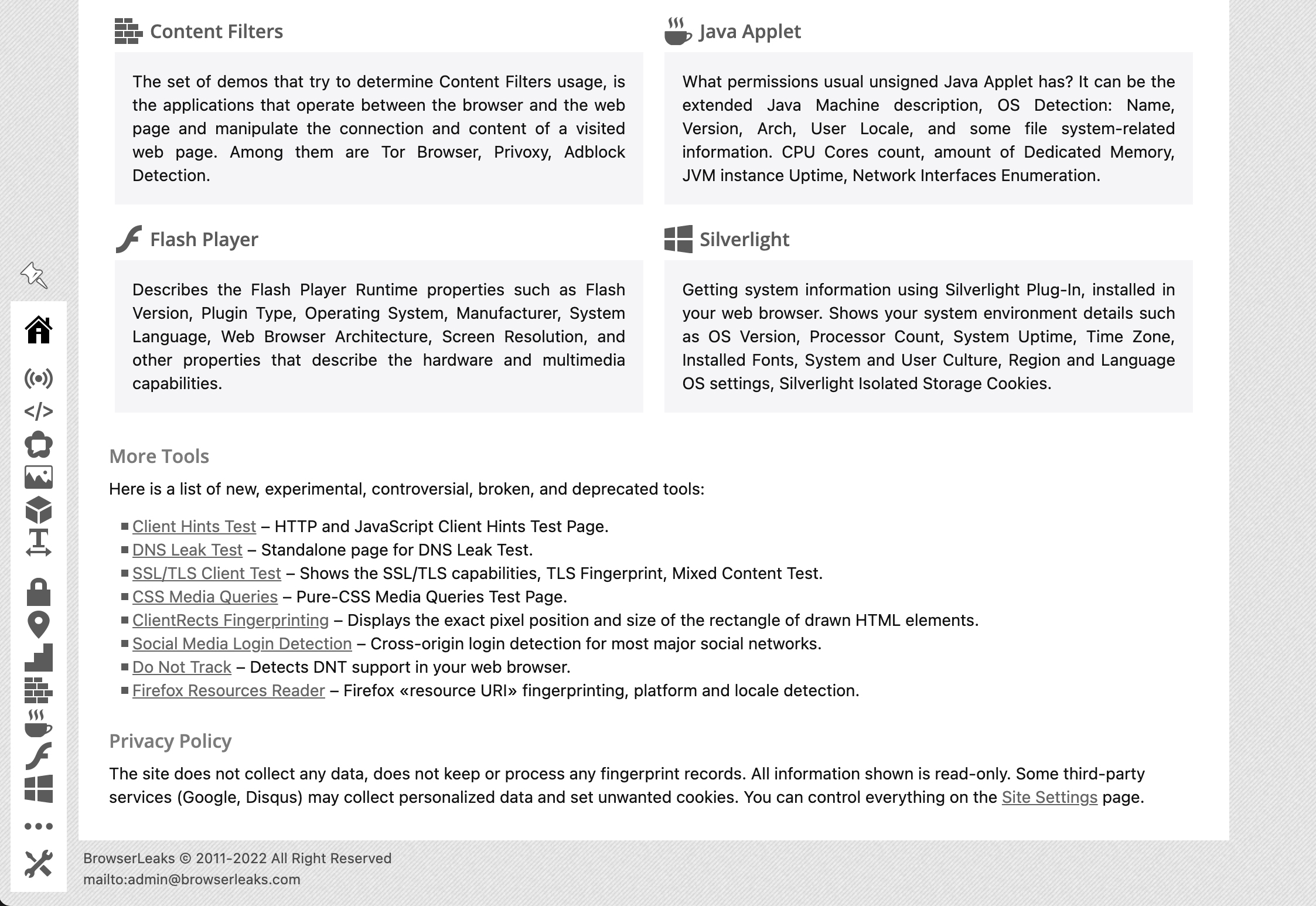
INFOSEC: browserleaks.com
 In order to mitigate flaws in your online security, it’s important to understand where the security gaps exist. BrowserLeaks provides over 20 tools that show users how their online data has been exposed and provide effective cyber hygiene tips. BrowserLeaks first demonstrates security flaws in your system, such as font fingerprinting, canvas fingerprinting, and WebRTC leaks. Before offering additional material and methods to protect oneself Browser Leaks explains how the flaws work. While this tool does not offer an all-encompassing methodology to ensure complete cyber hygiene, BrowserLeaks does powerfully demonstrate the importance of cyber hygiene.
In order to mitigate flaws in your online security, it’s important to understand where the security gaps exist. BrowserLeaks provides over 20 tools that show users how their online data has been exposed and provide effective cyber hygiene tips. BrowserLeaks first demonstrates security flaws in your system, such as font fingerprinting, canvas fingerprinting, and WebRTC leaks. Before offering additional material and methods to protect oneself Browser Leaks explains how the flaws work. While this tool does not offer an all-encompassing methodology to ensure complete cyber hygiene, BrowserLeaks does powerfully demonstrate the importance of cyber hygiene.
Have an OSINT tip for us? Contact us, and we will consider reviewing it in future posts!
 Like what you’re reading? Check out Hg’s monthly webinars!
Like what you’re reading? Check out Hg’s monthly webinars!
Throughout the year, Hetherington Group offers monthly live webinars on current investigative tactics involving social networks, search engines, due diligence, the dark web, and other related topics. Participants should have some basic experience of the topic, as all programs are offered at an intermediate level, unless otherwise noted.